TOKYO, Feb 7, 2024 – (JCN Newswire) – NEC Corporation (TSE: 6701) has developed a technology that strengthens the security of supply chains by detecting vulnerabilities in software from the binary code(1) of executable files, without the need for source code. This technology automates part of the static analysis of software for which source code is not available, which previously had to be done by experts, thereby reducing the time for static analysis by 40%.
Background
In recent years, supply chains in all industries have been expanding and becoming more complex due to digital transformation (DX) and globalization. Under these circumstances, there is a growing concern about cyberattacks targeting vulnerabilities and malicious functions being introduced in the supply chain, which has made ensuring the safety of software throughout the supply chain an urgent issue. In particular, government agencies and critical infrastructure providers are required to take measures to prevent backdoors and other malicious functions from being introduced into their products and systems when procuring and installing products and systems in accordance with revised laws and regulations.This newly developed technology will enhance NEC’s risk hunting service(2) in which security specialists (*3) conduct security risk assessments of a customer’s software and systems while considering the impact on their business.
Technology overview
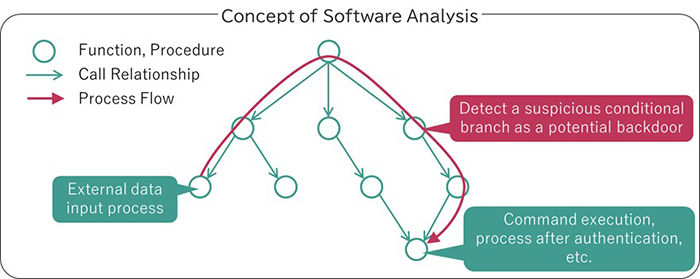
While general techniques for static analysis of software target source code, this technique performs static analysis on binary code, which is the executable form of software. In particular, it tracks which processes within the software use external data and detects suspicious implementations that may be backdoors capable of influencing the control of sensitive processes such as command execution.
Features of the technology
1. Software without source code can be inspected
In the past, source code was not available for some software, and in such cases, the means to check the safety of software were limited, such as manual inspections by experts. Since this technology can inspect binary code, it is possible to inspect the safety of software for which source code is not available.
2. Addresses concerns about build environment (*4) pollution
In the past, it was difficult to detect vulnerabilities and malicious functions introduced during the build process, even when source code was available, such as for in-house developed software. Since this technology inspects the binary code after it is built, it is possible to inspect for safety, including problems caused by the build environment.
3. Enables uniformity of inspection quality
In the past, it was difficult to inspect software, especially in binary format, and inspection quality tended to vary depending on the skill of the inspector. This technology automates part of the inspection process, thus reducing the need for human resources and ensuring a certain level of inspection quality. It also makes it possible to explain the safety of the company’s systems to third parties, such as regulatory authorities and shareholders, with evidence. Furthermore, the automation of part of the inspection is expected to reduce the time required for static analysis by 40%.NEC aims to apply this technology to risk hunting services by the end of FY2024. This will enhance safety inspections of software procured and delivered in the supply chain, contributing to the construction of safer and more secure systems and the strengthening of supply chain security.
(1) Data expressed only in binary numbers of 0s and 1s so that computers can process it directly.
(2) Risk Hunting Service (Japanese text only)https://jpn.nec.com/cybersecurity/service/professional/risk_hunting/index.html
(3) Security specialists (Japanese text only)https://jpn.nec.com/cybersecurity/advantage/specialist/profile2-2.html
(4) An environment that converts source code written in a programming language and generates an executable file written in binary code.Share
About NEC CorporationNEC Corporation has established itself as a leader in the integration of IT and network technologies while promoting the brand statement of “Orchestrating a brighter world.” NEC enables businesses and communities to adapt to rapid changes taking place in both society and the market as it provides for the social values of safety, security, fairness and efficiency to promote a more sustainable world where everyone has the chance to reach their full potential. For more information, visit NEC at https://www.nec.com.
Topic: Press release summary
Source: NEC Corporation
Sectors: CyberSecurity
http://www.acnnewswire.com
From the Asia Corporate News Network
Copyright © 2024 ACN Newswire. All rights reserved. A division of Asia Corporate News Network.
Source : ACN Newswire


